Azure Cloud Fundamentals to Real-World Infrastructure
Hands-On Learning Path
Microsoft Azure is a leading cloud platform for building secure, scalable, and production-ready infrastructure for enterprises and startups alike.
This Azure learning hub is designed to guide you from cloud fundamentals to real-world Azure implementations, using hands-on labs, diagrams, and practical examples. It is not a collection of disconnected tutorials; it is a structured learning path.
If your goal is to understand Azure properly, not just follow commands, this page shows you exactly where to start and how to progress.
What You’ll Learn on This Page
By following this Azure learning path, you will understand:
- Core cloud computing concepts used in Azure
- Azure networking fundamentals (VNets, subnets, tagging)
- Infrastructure as Code principles using Terraform
- How real Azure environments are structured in production
- How these skills map to cloud engineering and DevOps roles
Step 1 - Cloud Fundamentals
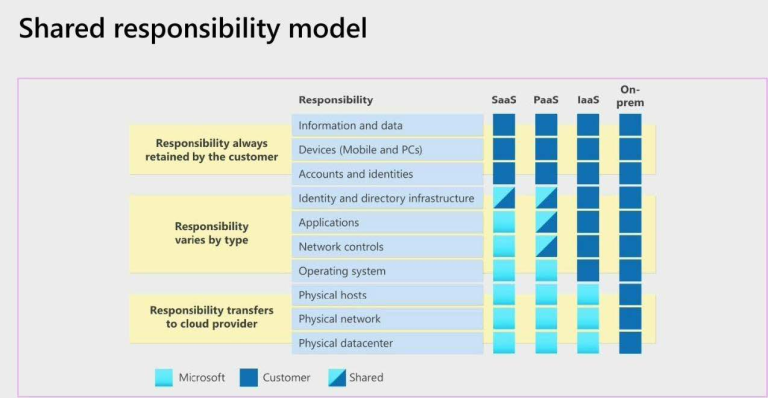
Before deploying anything in Azure, it’s important to understand what cloud computing actually is and how Azure fits into the broader cloud ecosystem.
This foundation prevents common beginner mistakes such as poor network design, insecure architectures, and inefficient scaling decisions.
👉 Start here:
In this guide, you’ll learn:
- What cloud computing really means (beyond buzzwords)
- Public vs private vs hybrid cloud
- Why Azure networking, security, and automation depend on these fundamentals
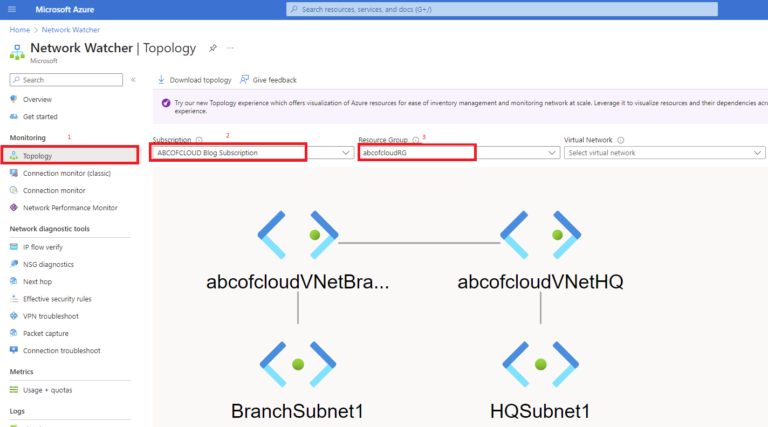
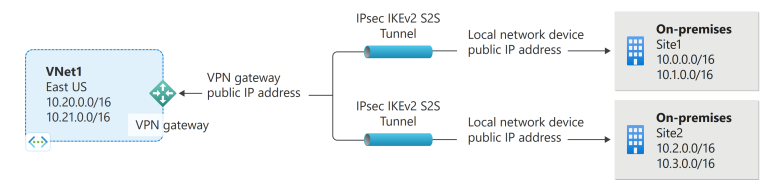
Step 2 - Azure Networking Fundamentals
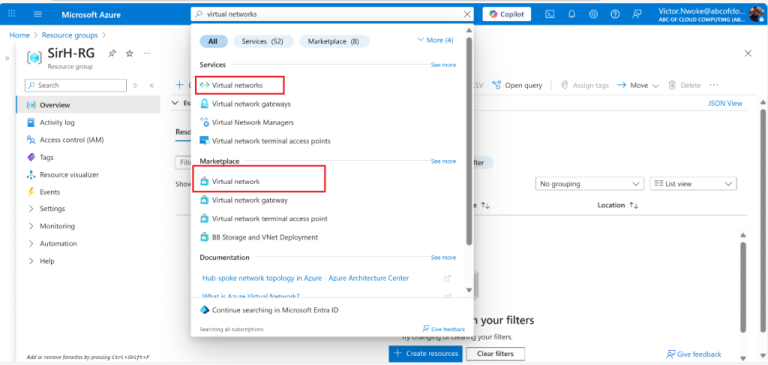
Networking is the backbone of every Azure environment.
Virtual networks, subnets, and resource tagging form the foundation for security, scalability, and governance.
This step focuses on building clean, production-ready Azure networks before introducing compute, security, or automation.
Core lab:
This lab covers:
- Azure Virtual Network design principles
- Subnet segmentation strategies
- Resource tagging for governance and cost management
- Transitioning from beginner concepts to production-ready design
⚠️ This step is a prerequisite for Azure compute, security, and automation topics.
Step 3 – Infrastructure as Code on Azure
Modern Azure environments are not built manually.
They are defined, versioned, and deployed using Infrastructure as Code (IaC). This ensures consistency, security, and repeatability across environments.
Terraform and Bicep are two of the most widely used tools for automating Azure infrastructure in real-world environments.
This step introduces how Azure infrastructure is deployed using code rather than clicks.
Core labs:
In this lab, you’ll learn:
- How Azure resources are represented in code
- Creating repeatable environments using Terraform
- Linking networking, security, and compute resources
- Why IaC is critical for DevOps and cloud engineering roles
- How Terraform and Bicep deploy Azure resources
- How monitoring and governance integrate into deployments
Step 4 – Azure Security, Identity & Governance
Secure Azure environments rely on strong identity controls, governance, and monitoring, not just firewalls.
This step focuses on protecting Azure resources using native Azure services and best practices.
Recommended topics:
These labs show how production environments enforce:
- Least-privilege access
- Governance at scale
- Operational visibility and alerting
Step 5 – Secure & Scalable Azure Architectures
Once the fundamentals, networking, and security are in place, you can move into secure and scalable infrastructure designs.
This step focuses on building environments that are resilient, repeatable, and production-ready.
Key labs include:
Step 6 – Real-World Azure Deployments
The final step demonstrates how Azure is used in real production scenarios.
These labs combine networking, compute, security, monitoring, and automation into complete environments.
Recommended advanced labs:
How These Skills Are Used in Real Azure Environments
In production environments, these concepts are combined to build:
- Secure application networks
- Scalable compute platforms
- Governed and auditable cloud infrastructure
- Automated deployment pipelines
These foundations are extended using tools such as:
- Azure PowerShell
- Azure Bicep
- Monitoring and alerting services
- Identity and access management
As you progress, you’ll naturally move into advanced Azure topics such as security hardening, scalable architectures, monitoring, and automation.
How to Use This Azure Learning Path
To get the most value from this section:
- Follow the steps in order if you are new to Azure
- Don’t skip networking and fundamentals
- Focus on understanding architecture, not memorising commands
- Reproduce labs in your own Azure subscription where possible
All content is educational and informational. No products or paid services are sold.
Closing
Azure is not just a collection of services; it is a platform built on networking, identity, governance, and automation.
This Azure learning path exists to help you understand how Azure environments are actually designed and operated, so your skills remain relevant, transferable, and production-ready.