Step-by-step lab: creating users, OUs, security groups, and group memberships using PowerShell
Managing users, organizational units (OUs), and security groups is one of the most common and most critical responsibilities in Windows-based enterprise environments. Yet many organizations still rely heavily on manual, click-based workflows through graphical tools like Active Directory Users and Computers (ADUC).
While ADUC is useful for learning and small environments, it quickly becomes inefficient and error-prone at scale.
PowerShell changes that.
In this hands-on lab, you’ll learn how to automate core Active Directory identity tasks using PowerShell the same way enterprise system administrators and infrastructure engineers do it in production environments.
By the end of this guide, you’ll understand not only how to automate Active Directory user and group management, but also why this approach is foundational for scalable identity, governance, and security.
Why Automate Active Directory with PowerShell?
Managing users and groups manually through graphical tools does not scale in enterprise environments. As organizations grow, repetitive point-and-click administration increases the risk of misconfiguration, inconsistent access control, and operational drift across the directory.
The Core Problem with Manual Administration
When user creation and access assignment rely on memory and manual steps:
-
Administrators apply permissions inconsistently
-
Users are placed in the wrong OUs
-
Group memberships become difficult to audit
-
Security policies drift over time
-
Documentation quickly becomes outdated
These issues are not caused by lack of skill; they are caused by process limitations.
Why PowerShell Is the Enterprise Standard
PowerShell provides a consistent, repeatable, and auditable way to manage Active Directory. Instead of relying on human memory and manual clicks, administrators define intent through code.
This approach aligns directly with modern infrastructure principles such as:
-
Role-Based Access Control (RBAC)
-
Least-privilege access
-
Automation-first operations
-
Infrastructure as Code (IaC)
If you’re new to structuring identity objects correctly, start with
👉 Managing Active Directory: Create OUs, Groups, and Users on Windows Server 2019 (Hyper-V Lab)
What This Lab Covers
In this step-by-step PowerShell lab, you will automate the following real-world Active Directory workflows:
-
Creating a new Active Directory user
-
Placing the user into a specific Organizational Unit (OU)
-
Creating a security group in a designated OU
-
Adding the user to the security group
-
Verifying objects and group memberships using PowerShell
These are the same tasks performed daily in enterprise IT environments but executed safely, consistently, and at scale.
🎥 Video Walkthrough
Lab Prerequisites
Before starting, ensure the following requirements are met:
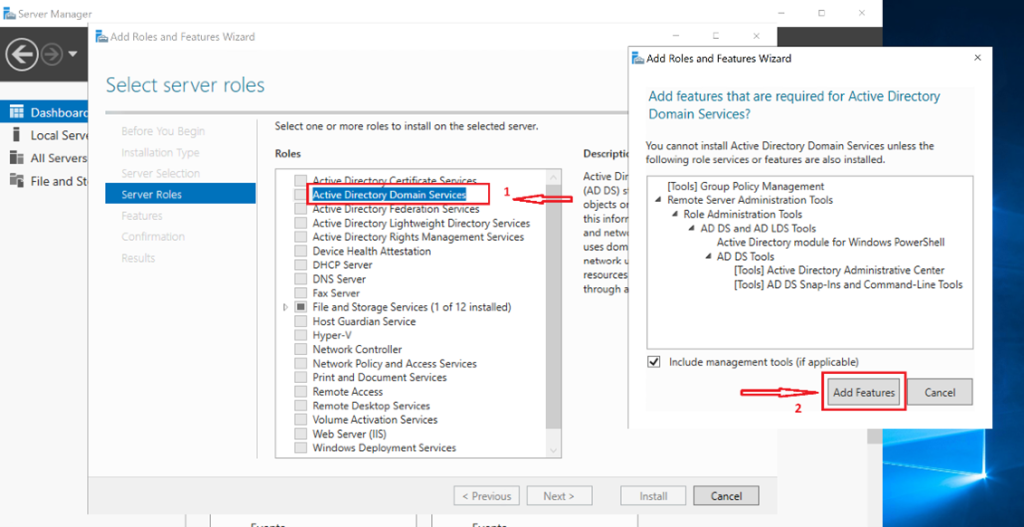
-
Active Directory Domain Services (AD DS) installed
👉 If not yet installed, see How to Install Active Directory Domain Services (AD DS) on Windows Server using Hyper-V (Step-by-Step Guide) -
PowerShell running with administrative privileges
-
RSAT / ActiveDirectory PowerShell module available
If your lab environment is not ready yet, first complete:
👉 Deploying Windows Server on Hyper-V with Static IP Configuration
👉 Step-by-Step Guide: Creating a Client Computer and Joining It to a Domain (Hyper-V Lab Setup)
Prerequisite (Run Once)
Verify that the Active Directory PowerShell module is available:
Run:
Import-Module ActiveDirectoryIf this command fails, install the RSAT tools or AD DS management features.
Step‑by‑Step PowerShell Implementation
Step 1: Create a New Active Directory User Using PowerShell
Objective: Automate user creation instead of using ADUC.
This command:
-
Defines user attributes
-
Specifies the correct OU
-
Enables the account immediately
PowerShell Command
New-ADUser `
-Name "John Doe" `
-GivenName "John" `
-Surname "Doe" `
-SamAccountName "jdoe" `
-UserPrincipalName "jdoe@humbletech.local" `
-Path "OU=Users,OU=HumbleTech,DC=humbletech,DC=local" `
-AccountPassword (ConvertTo-SecureString "P@ssw0rd123!" -AsPlainText -Force) `
-Enabled $true
✅Result:
The user is created directly in the correct OU, ready for policy application and group membership.
📌 Why OU placement matters:
Group Policy Objects (GPOs), delegation boundaries, and administrative controls are all OU-based.
To understand how OU design impacts policy enforcement, see:
👉 How to Configure Desktop Backgrounds, Power Settings, and Legal Notices Using Group Policy
Step 2: Assign the User to a Specific Organizational Unit (OU)
If the user already exists and needs to be moved:
Move-ADObject `
-Identity "CN=John Doe,CN=Users,DC=humbletech,DC=local" `
-TargetPath "OU=Users,OU=HumbleTech,DC=humbletech,DC=local"
Alternative (recommended): Recommended Verification
Get-ADUser jdoe | Select-Object DistinguishedName🔐 Enterprise insight:
OU placement controls which policies apply and who can administer the object. Poor OU hygiene leads directly to security gaps.
Step 3: Create a New Security Group in a Designated OU
Objective: Automate group creation for RBAC-based access control.
PowerShell Command
New-ADGroup `
-Name "HR-Security-Group" `
-SamAccountName "HR-Sec-Group" `
-GroupCategory Security `
-GroupScope Global `
-Path "OU=Groups,OU=HumbleTech,DC=humbletech,DC=local" `
-Description "Security group for HR users"Best-Practice Notes
-
Security group, not distribution
-
Global scope (recommended for permissions)
-
Created directly inside the Groups OU
To see how group-based permissions integrate with file systems, read:
👉 How to Configure Secure File System Management with NTFS Permissions and Mapped Drives in a Windows Server Domain (Lab Guide)
Step 4: Add the User to the Security Group
Objective: Grant access through group membership instead of direct permissions.
-
Add user to security group
-
Verify membership
PowerShell Command
Add-ADGroupMember `
-Identity "HR-Security-Group" `
-Members jdoe
Verify Membership
Get-ADGroupMember "HR-Security-Group"Optional Verification Commands
Confirm User Exists
Get-ADUser jdoeConfirm Group Exists
Get-ADGroup "HR-Security-Group"Confirm User’s Group Membership
Get-ADPrincipalGroupMembership jdoe | Select NamePro Tip: Always Assign Permissions to Groups
In enterprise environments, permissions should never be assigned directly to users.
This PowerShell-driven workflow enforces:
-
Role-based access control (RBAC)
-
Easier audits
-
Cleaner permission models
-
Faster onboarding and offboarding
This principle also underpins secure Group Policy design, such as:
👉 How to Restrict USB and Removable Storage Devices using Group Policy in Active Directory
Why This Matters in Enterprise Environments
Automating Active Directory with PowerShell:
-
Reduces human error
-
Improves consistency
-
Saves administrative time
-
Scales across hundreds or thousands of users
-
Forms the foundation for identity governance and security automation
When combined with proper infrastructure planning, including redundant domain controllers, it becomes even more powerful:
👉 How to Add a Secondary Domain Controller to an Existing Domain (Hyper-V Lab)
Common Mistakes & Troubleshooting (PowerShell + Active Directory)
Even simple Active Directory automation can fail if prerequisites, permissions, or object paths are incorrect. Below are the most common issues administrators encounter when managing users and groups with PowerShell, along with clear explanations and fixes.
❌ Mistake 1: Import-Module ActiveDirectory Fails
Symptom
Import-Module : The specified module 'ActiveDirectory' was not loaded
Cause
The Active Directory PowerShell module is not installed. This typically happens when:
-
RSAT tools are missing
-
AD DS management features were not installed
-
You are running PowerShell on a non-management server
Fix
-
On a domain controller, install AD DS management tools
-
On a member server or admin workstation, install RSAT
Why this matters
PowerShell cmdlets like New-ADUser, New-ADGroup, and Get-ADUser are not available without this module.
❌ Mistake 2: “Access Is Denied” Errors
Symptom
Discover more from Humble Cloud Tech
Subscribe to get the latest posts sent to your email.